Google releases emergency security patch for actively exploited zero-day vulnerability that could give attackers full system access through a simple webpage visit
 Critical Chrome zero-day vulnerability actively exploited in the wild. Source: Cyber Security News
Critical Chrome zero-day vulnerability actively exploited in the wild. Source: Cyber Security News
In a critical security alert that demands immediate action, Google has released an emergency update for its Chrome browser to address six security vulnerabilities, including a dangerous zero-day flaw that cybercriminals are actively exploiting to break out of the browser’s protective sandbox and compromise entire systems.
🎯 The Threat: A Sophisticated Sandbox Escape Attack
The most serious vulnerability, designated CVE-2025-6558, represents a nightmare scenario for internet users: a high-severity flaw with an 8.8 CVSS score that allows attackers to escape Chrome’s security sandbox simply by tricking users into visiting a malicious webpage. No downloads, no clicks, no user interaction required beyond the initial page visit.
“Insufficient validation of untrusted input in ANGLE and GPU in Google Chrome prior to 138.0.7204.157 allowed a remote attacker to potentially perform a sandbox escape via a crafted HTML page.” — National Vulnerability Database (NVD)
What Makes This Attack So Dangerous?
Unlike typical browser vulnerabilities that remain contained within the browser’s security boundaries, CVE-2025-6558 enables what security experts call a “sandbox escape.” This means:
- Complete System Compromise: Attackers can break free from Chrome’s protective barriers
- Silent Exploitation: No user interaction required beyond visiting a webpage
- Perfect for Targeted Attacks: Ideal for nation-state actors and sophisticated cybercriminals
- Universal Impact: Affects billions of Chrome users worldwide
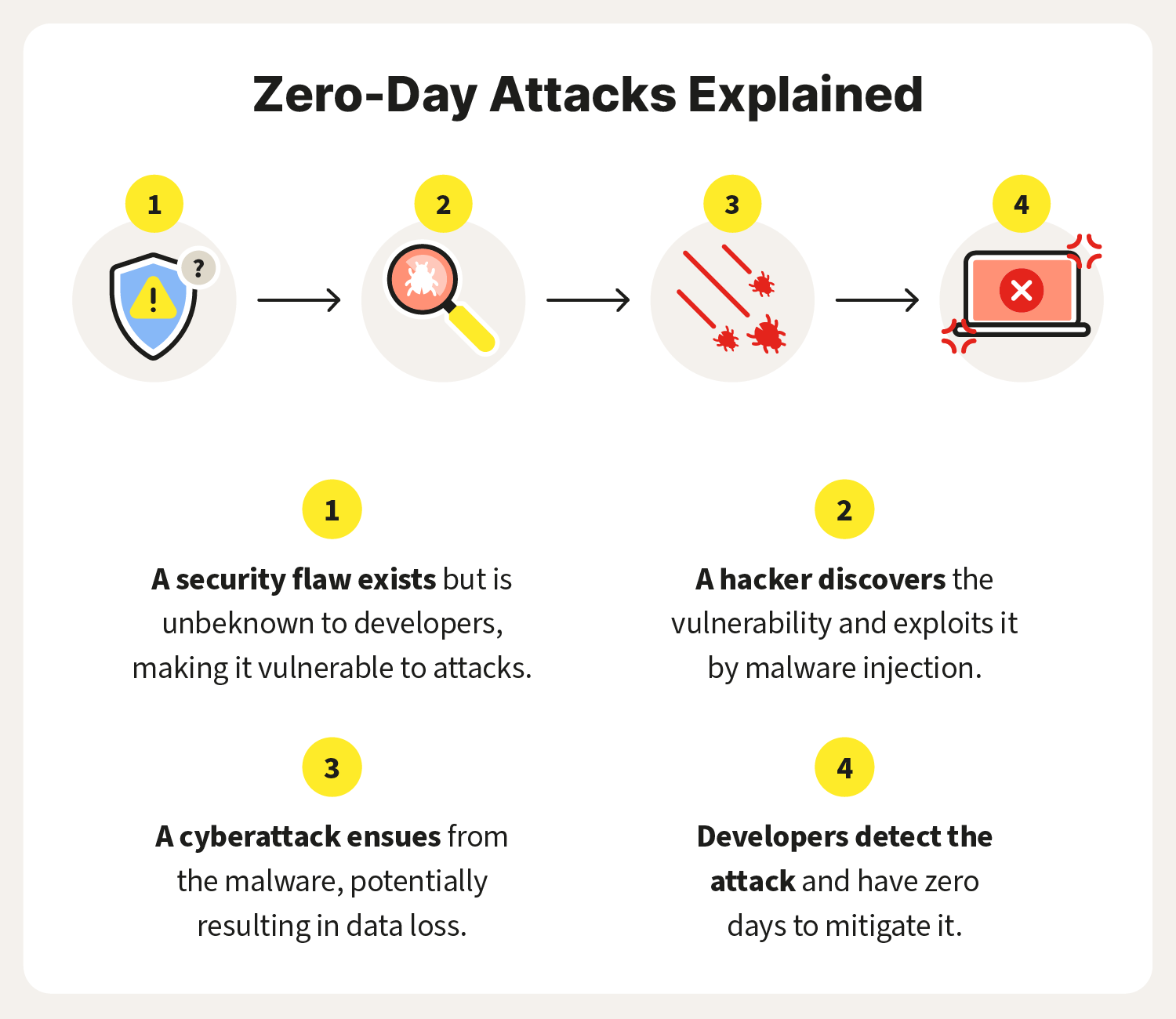 The lifecycle of zero-day attacks shows how quickly threats can spread before patches are available. Source: Norton
The lifecycle of zero-day attacks shows how quickly threats can spread before patches are available. Source: Norton
🔍 Technical Deep Dive: Understanding the ANGLE Vulnerability
The vulnerability lies within Chrome’s ANGLE (Almost Native Graphics Layer Engine) component, a critical translation layer that converts graphics commands between different systems. As security researchers at Malwarebytes explain, ANGLE acts as a universal translator for 3D graphics, powering everything from WebGL games to interactive web applications across Windows, Mac, and Android devices Malwarebytes.
Why ANGLE Vulnerabilities Are So Critical
ANGLE’s unique position in Chrome’s architecture makes it a high-value target:
- Universal Access: ANGLE processes GPU commands from any website using WebGL
- Low-level Operations: Direct interaction with graphics drivers and system hardware
- Trusted Component: Operates with elevated privileges within Chrome’s architecture
- Cross-Platform Impact: Affects Chrome across all operating systems
According to security analysis from SOC Prime, “vulnerabilities in this component can let attackers escape Chrome’s sandbox by abusing low-level GPU operations that browsers usually keep isolated, making this a rare but powerful path to deeper system access” SOC Prime.
🏴☠️ Active Exploitation: Nation-State Involvement Suspected
Google’s Threat Analysis Group (TAG) discovered CVE-2025-6558 on June 23, 2025, with the vulnerability being actively weaponized in real-world attacks. The involvement of TAG—a team that specifically focuses on nation-state actors and sophisticated spyware operations—strongly suggests this zero-day is being used in targeted espionage campaigns.
The Growing Zero-Day Crisis
This latest Chrome vulnerability represents the fifth actively exploited zero-day in Chrome during 2025, highlighting an alarming trend:
- March 2025: CVE-2025-2783 - Sandbox escape used in Russian government targeting
- May 2025: CVE-2025-4664 - Cross-site account hijacking attacks
- June 2025: CVE-2025-5419 - V8 engine exploitation
- July 2025: CVE-2025-6554 - Type confusion in V8 JavaScript engine
- July 2025: CVE-2025-6558 - Current ANGLE/GPU sandbox escape
As noted by BleepingComputer, “zero-day exploitation has been steadily increasing over the past four years,” with exploits now responsible for 33% of initial attack vectors in 2025 BleepingComputer.
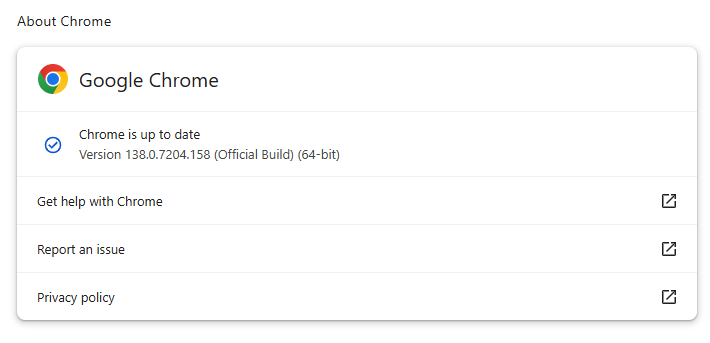 Always verify your Chrome version shows the latest security updates. Source: Malwarebytes
Always verify your Chrome version shows the latest security updates. Source: Malwarebytes
⚡ Immediate Action Required: How to Protect Yourself
Step 1: Update Chrome Immediately
Target Versions:
- Windows/Mac: 138.0.7204.157 or 138.0.7204.158
- Linux: 138.0.7204.157
Quick Update Method:
- Click the three-dot menu (⋮) in Chrome
- Navigate to Settings > About Chrome
- Chrome will automatically check and download updates
- Click Relaunch when prompted
Alternative Method:
- Type
chrome://settings/helpin your address bar - Follow the update prompts
Step 2: Verify Your Update
Ensure your Chrome version matches or exceeds the patched versions listed above. If you’re running an older version, repeat the update process or restart Chrome completely.
Step 3: Consider Additional Protections
- Enable Enhanced Safe Browsing: Chrome Settings > Privacy and Security > Security
- Keep Extensions Updated: Malicious extensions can bypass some protections
- Consider Browser Isolation: Use virtual machines for high-risk browsing
🌐 Beyond Chrome: Protecting Chromium-Based Browsers
The vulnerability affects all Chromium-based browsers, including:
- Microsoft Edge
- Brave Browser
- Opera
- Vivaldi
- Samsung Internet
Users of these browsers should apply security updates as they become available from their respective vendors.
 The interconnected nature of Chromium-based browsers means vulnerabilities can have widespread impact. Source: OPSWAT
The interconnected nature of Chromium-based browsers means vulnerabilities can have widespread impact. Source: OPSWAT
🎯 Understanding the Broader Threat Landscape
The Rise of Graphics-Based Attacks
Security experts are observing increased targeting of graphics components in browsers. As noted in The Hacker News analysis, “issues like this often fall under broader categories like GPU sandbox escapes, shader-related bugs, or WebGL vulnerabilities” The Hacker News.
Why Graphics Vulnerabilities Matter
Modern web applications increasingly rely on:
- WebGL for 3D graphics
- Hardware-accelerated video processing
- GPU-based cryptocurrency mining
- Advanced visual effects and animations
This expanded attack surface creates new opportunities for sophisticated threat actors to exploit graphics processing components.
🔮 What Security Experts Are Saying
“For most users, a sandbox escape like this means that visiting a malicious site is sufficient to potentially break out of the browser’s security bubble and interact with the underlying system. This is especially critical in targeted attacks where just opening a webpage could trigger a silent compromise.” — The Hacker News Security Analysis
“Defending against zero-day vulnerability exploitation remains a strategic challenge for defenders. True resilience depends on vendors’ and organizations’ ability to quickly counter evolving threats.” — SOC Prime Threat Intelligence
🚀 Proactive Security Measures for Organizations
Enterprise Recommendations
- Immediate Patch Deployment: Use automated update systems to ensure rapid Chrome updates
- Network Monitoring: Implement detection rules for graphics-related exploit attempts
- Browser Isolation: Deploy remote browser isolation for high-risk users
- User Education: Train employees on identifying potential zero-day attack vectors
Detection Strategies
Security teams should monitor for:
- Unusual GPU process activity
- Abnormal ANGLE component behavior
- Sandbox escape attempt indicators
- WebGL-related exploitation patterns
 Security teams must implement comprehensive monitoring for graphics-based exploits. Source: SecureITWorld
Security teams must implement comprehensive monitoring for graphics-based exploits. Source: SecureITWorld
📊 The Bigger Picture: Chrome’s 2025 Security Challenges
Zero-Day Statistics
- 5 actively exploited zero-days in Chrome during 2025
- 75 zero-day vulnerabilities reported globally in 2024
- 33% of attacks now begin with exploit-based initial access
- Increasing sophistication in nation-state attack techniques
Industry Response
The frequency of Chrome zero-days has prompted:
- Enhanced bug bounty programs with higher rewards
- Accelerated patch deployment processes
- Improved sandbox technologies in development
- Closer collaboration with security researchers
🎬 Conclusion: Stay Vigilant, Stay Updated
The CVE-2025-6558 vulnerability represents a critical reminder that browser security requires constant vigilance. With attackers increasingly targeting graphics components and sandbox escape vulnerabilities, users and organizations must prioritize rapid security updates and comprehensive protection strategies.
Key Takeaways:
✅ Update Chrome immediately to version 138.0.7204.157/.158
✅ Verify your update completed successfully
✅ Enable enhanced security features in Chrome
✅ Monitor for additional updates from Chromium-based browser vendors
✅ Implement organizational security policies for rapid patch deployment
The battle against zero-day exploits continues to intensify, but staying informed and maintaining current security patches remains our strongest defense against these sophisticated threats.
📚 Additional Resources
- Chrome Security Updates
- CISA Known Exploited Vulnerabilities Catalog
- Google Chrome Enterprise Security Guide